Intrusion Detection Systems
Waterfall for intrusion detection systems for safe OT-network intrusion detection
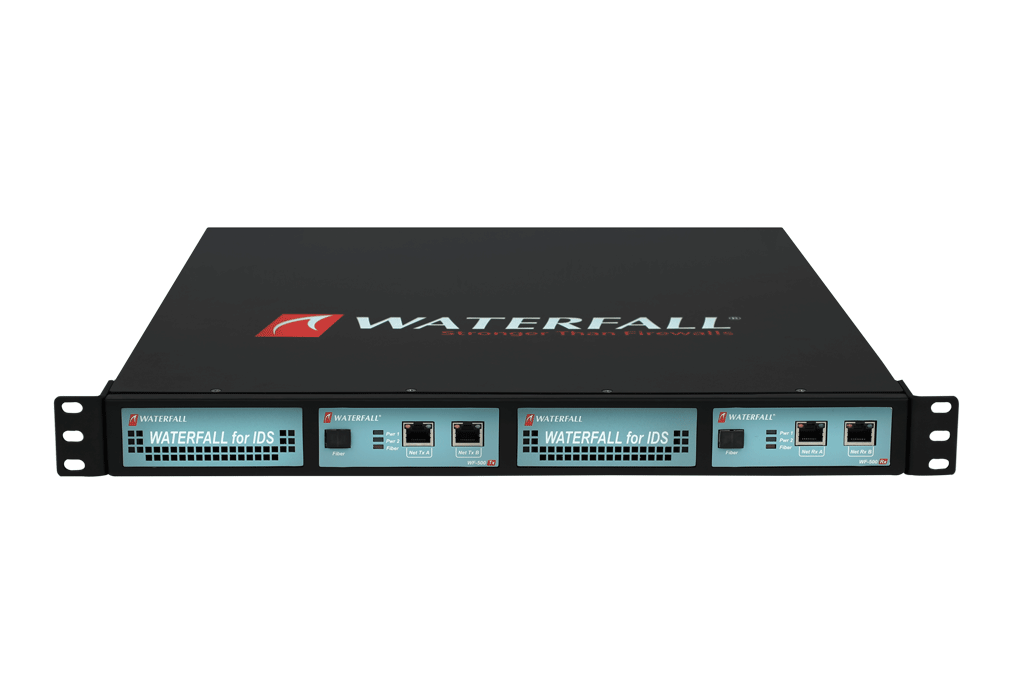
Waterfall for Intrusion Detection Systems
Waterfall for Intrusion Detection Systems (IDS) enables network intrusion sensors to monitor operations technology (OT) and industrial control system (ICS) networks without risk to the monitored networks. Waterfall for IDS is a hardware-enforced, physical barrier that prevents remote attacks, malware, DOS attacks, ransomware and human errors originating on external networks from compromising or impairing industrial operations.

Waterfall for IDS replicates traffic captures from OT mirror and SPAN ports, to network IDS sensors on IT networks. Waterfall for IDS deploys transparently between mirror ports and sensors, without the vulnerabilities that always accompany direct connections of IT equipment to OT networks. Waterfall for IDS is a combination of hardware and software and is based on Waterfall’s industry-leading Unidirectional Security Gateway technology. Waterfall for IDS hardware is physically able to transmit information in only one direction, from the OT switch to the IT sensor. Waterfall for IDS is physically incapable of propagating any virus, DOS attack, human error or remote-control attack back into the protected OT network. With Waterfall for IDS in place, industrial enterprises can confidently host OT network intrusion sensors on IT networks where the sensors are easily managed and updated by central SOC analysts, without risk to industrial operations. Waterfall for IDS is partnered with the following Intrusion Detection vendors: CyberX, ForeScout, Dragos, Radiflow, Splun and FireEye.
Features
Safe Intrustion Detection
Safe port mirroring from OT to IT, without introducing Internet-based cyber threats to monitored networks.
Easy Management of IDS Sensors
Network sensors can be deployed on IT networks for easy management, without risk to monitored OT networks.
Easy Integration with SOC
Supports stand-alone operations and integration with industry-leading SIEM/SOC solutions.
No new ICS hosts
Flexible hardware configurations include options where no new hosts or software need be introduced to sensitive ICS networks.