About company
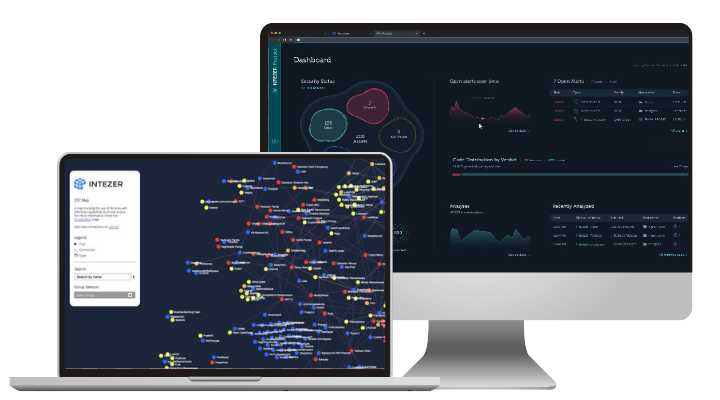
Intezer reduces the time and resource pressures on SOC and IR teams, by automatically classifying threats in easy-to-understand reports that get archived for knowledge retention and connecting separate incidents.With more automation in your toolset, you can eliminate time wasted on false positives, reduce staff turnover, close skill gaps, and retain historical data.
 />
/>
Key benefits
Intezer functions as your Tier 1+2 SOC/IR analysts, enabling you to focus only on the incidents that matter and help you to actively hunt for thousands of threat actors and campaigns
/>
Values
- Automated alert triage, response and hunting
- Reduce likelihood of a security breach
- Reduce skill gaps and cost of talent
- Automated decision-making by previously seen threats
Problem-solution
- Lots of false positives / Alert triage: automatically analyze files, URLs, and machines to classify and prioritize threats. Intezer has a false positive rate of 0.2%
- Low incident response / Incident Response: teams can see an immediate improvement in Mean Time to Respond (MTTR), with automated extraction of IoCs and detection content.
- Loss of knowledge / Knowledge Retention: with access to a central source of knowledge for all micro-artifacts ever seen before in the past, IR teams can easily make connections between separate incidents and even new analysts can provide deeper, historic context.
Connect your alert pipelines (like EDR, SOAR, SIEM), so Intezer can collect data to offer advice and help you automatically triage alerts, respond, and hunt threats.
Countries
Softprom is the official distributor of this vendor in the territory of







 Armenia
Armenia Azerbaijan
Azerbaijan Bulgaria
Bulgaria Czech Republic
Czech Republic Georgia
Georgia Hungary
Hungary Kazakhstan
Kazakhstan Moldova
Moldova Poland
Poland Slovakia
Slovakia Tajikistan
Tajikistan Ukraine
Ukraine Uzbekistan
Uzbekistan