About company
Softprom is an authorized Netwrix distributor in Poland and a value-added IT distributor operating since 1999 across 33 countries with 120+ vendors and 1,200+ IT solutions in portfolio. We deliver the full Netwrix product line — built around the Netwrix 1Secure™ platform — to Polish enterprises, public-sector organizations, banks, and managed service providers (MSPs), with local pre-sales engineering, pilot programs, and post-sale support.
Netwrix is a US-based cybersecurity vendor headquartered in Frisco, Texas, trusted by 13,000+ organizations worldwide, including 120+ Fortune 500 companies, with a 95% customer satisfaction rating. Its identity-first approach unifies data security and identity security in one control plane — closing the gap attackers exploit between overprivileged accounts and sensitive data.
Through Softprom, Polish customers get Netwrix solutions aligned to local compliance frameworks — RODO NIS 2 / KSC DORA KNF Rekomendacja D ISO 27001 — and supported by 30+ certified cybersecurity engineers across our 14 regional offices in Central and Eastern Europe, the Caucasus, and Central Asia.
Attackers exploit the blind spot between identity and data, where overprivileged access meets sensitive information. Netwrix 1Secure unifies identity risk detection and data exposure visibility into a single control plane — so identity abuse never becomes a data disaster.
The Netwrix 1Secure™ Platform
One platform. Three security disciplines unified. Replace siloed tools with a single command center that connects identities, data, and endpoints.
Data Security
Data Security Posture Management (DSPM), Data Access Governance (DAG), Data Loss Prevention (DLP), and Data Discovery & Classification — discover sensitive data, enforce least-privilege access, prevent exfiltration.
Identity Security
Identity Threat Detection & Response (ITDR), Identity Governance & Administration (IGA), Identity Security Posture Management (ISPM), Privileged Access Management (PAM), and Directory Security for Active Directory and Entra ID.
AI Governance
Protect sensitive data accessed by Microsoft 365 Copilot and other LLM tools. Discover overshared SharePoint and OneDrive content before Copilot rollout, apply sensitivity labels, monitor risky AI interactions in real time.
Netwrix capabilities — 10 control areas in one platform
Discover, prioritize, and remediate data exposure across cloud, on-prem, and hybrid stores. Continuous visibility into where sensitive data lives, who can access it, and how the access risk is changing — with AI-driven prioritization that highlights the combinations attackers actually exploit.
Reduce breach risk by enforcing least-privilege access to sensitive data across file servers, SharePoint, OneDrive, Teams, and cloud storage. Identify excessive permissions, stale access, and toxic combinations — then remediate at scale.
Block sensitive data exfiltration across every endpoint — Windows, macOS, and Linux. Device control, content-aware filtering, and policy enforcement for USB, cloud uploads, email, and printing, delivered by Netwrix Endpoint Protector.
Automatically inventory and label sensitive, regulated, and mission-critical data — including PII under RODO, financial records under DORA, and health data — across on-prem repositories, Microsoft 365, and cloud storage.
Protect sensitive data accessed by Copilot and other generative AI tools. Scan SharePoint, OneDrive, and Teams for overshared and unclassified files before Copilot deployment, apply sensitivity labels, enforce least-privilege access, and monitor Copilot interactions for risky data exposure.
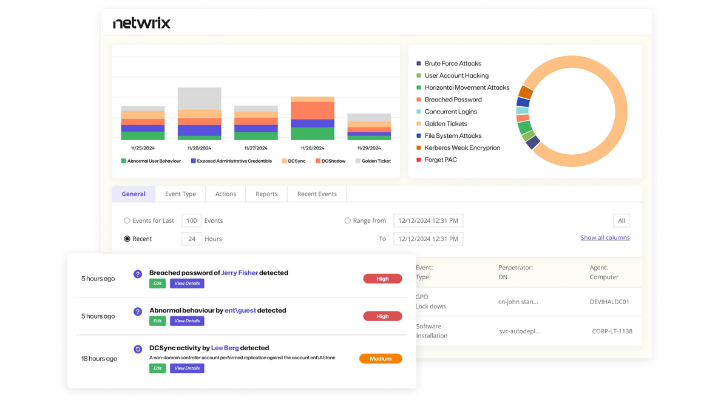
Prevent, detect, and respond to identity-driven attacks in real time. Behavioral analytics for Active Directory, Entra ID, and privileged sessions — surfacing Kerberoasting, DCSync, Golden Ticket, password spraying, and lateral-movement patterns.
Automate the joiner-mover-leaver lifecycle for every identity. Self-service access requests, automated provisioning to 100+ applications, periodic access certifications, and audit-ready evidence for RODO and ISO 27001.
Continuously assess and close identity-system weaknesses — misconfigurations in Active Directory, Entra ID Conditional Access gaps, unprotected service accounts, AD Certificate Services exposures, and non-human identity risks.
Eliminate standing privileges with just-in-time (JIT) access, audit every elevated session, and remove the attack surface created by always-on admin accounts. Delivered by Netwrix Privilege Secure for zero-standing-privilege architecture.
Monitor identity systems and recover quickly from directory-level attacks. AD posture scoring with Netwrix PingCastle, change auditing with Netwrix Auditor, and disaster-recovery readiness for ransomware-impacted domains.
Netwrix products available through Softprom in Poland
Netwrix Auditor
Cross-platform change auditing and behavior analytics for Active Directory, Microsoft 365, file servers, SharePoint, and databases. Answers who changed what, when, and from where — with audit-ready reports for RODO, NIS 2, and DORA.
Netwrix Access Analyzer
Effective-permissions analysis and access-risk remediation. Identifies who has access to which sensitive data, surfaces excessive privileges, and automates least-privilege enforcement across file shares, Microsoft 365, and cloud storage.
Netwrix PingCastle
Active Directory security assessment and continuous AD posture scoring. Industry-standard AD risk-scoring methodology used by 10,000+ organizations to map and remediate domain-level attack paths.
Netwrix Endpoint Protector
Cross-platform endpoint DLP for Windows, macOS, and Linux. Device control, content-aware filtering, eDiscovery, and enforced encryption — chosen by Samsung R&D Institute for cross-platform endpoint coverage.
Netwrix Privilege Secure
Just-in-time, zero-standing-privilege PAM. Provision elevated access only when needed, record every privileged session, and eliminate the always-on admin accounts that ransomware operators target first.
Netwrix Identity Manager
Lifecycle management, access requests, and certifications for hybrid identities. Automates joiner-mover-leaver workflows across Active Directory, Entra ID, and 100+ business applications.
How Netwrix 1Secure works
Discover#1
Connect Netwrix 1Secure to your environment — Active Directory, Entra ID, Microsoft 365, file servers, cloud storage. Within hours the platform inventories identities, classifies sensitive data, and maps effective permissions across the entire estate.
Prioritize#2
Context-aware AI correlates identity weaknesses with data exposure and highlights the combinations attackers exploit first. You see a ranked list of what to fix — not 10,000 alerts to triage.
Remediate#3
Apply AI-guided fixes from the 1Secure command center: revoke excessive permissions, label sensitive data, rotate privileged credentials, enforce JIT access, close AD misconfigurations. Workflows are automated where safe, approved where critical.
Monitor & respond#4
Continuous monitoring across hybrid systems, smart alerts on real threats, automated response playbooks, and audit-ready evidence for RODO, NIS 2 / KSC, and DORA — from a single 360° dashboard.
Use cases for the Polish market
From banks under KNF supervision to manufacturers in NIS 2 scope — Netwrix maps directly to Polish regulatory and operational requirements.
Active Directory hardening
Score and remediate AD security posture with Netwrix PingCastle. Close attack paths to domain admin before Microsoft 365 Copilot rollout, ransomware operators, or auditors find them.
Microsoft 365 Copilot Readiness
Discover and remediate overshared SharePoint, OneDrive, and Teams data before enabling Copilot. Apply sensitivity labels, enforce least-privilege access, and prevent Copilot from surfacing data employees should not see.
RODO & GDPR audit
Locate personal data across the estate, prove who accessed it, and produce evidence packs for UODO (Urząd Ochrony Danych Osobowych) and internal Data Protection Officers — without manual report assembly.
NIS 2 & Ustawa o KSC
Meet identity, access-control, and incident-detection requirements of NIS 2 and the Polish Krajowy System Cyberbezpieczeństwa Act for Operatorzy Usług Kluczowych (OUK) and important entities.
DORA for the financial sector
Operational-resilience controls, ICT third-party risk monitoring, and identity governance for Polish banks, insurers, and investment firms under KNF supervision — aligned to DORA from Jan 2025.
Zero Trust for distributed teams
Least-privilege access to data, continuous identity verification, and just-in-time privileges for hybrid workforces — without rebuilding the network.
Shadow AI & Copilot data exposure
Discover unsanctioned generative-AI usage, classify data flowing into LLMs, and enforce label-based access controls before sensitive records leak into prompts.
Mergers, acquisitions & divestitures
Fast directory consolidation, permission cleanup, and data classification across merging tenants — collapse two AD forests into one without inheriting hidden access risks.
Managed Service Providers
Multi-tenant Netwrix 1Secure for Polish MSPs serving SMB and mid-market clients. Centralized dashboard, per-tenant reporting, and a partner program built for monthly recurring revenue.
Netwrix Auditor vs. Netwrix Access Analyzer — which one do you need?
|
Capability comparison |
Netwrix Auditor | Netwrix Access Analyzer |
|---|---|---|
| Change auditing across AD, M365, file servers, databases | + | |
| User behavior analytics & anomaly detection | + | |
| Compliance reporting (RODO, NIS 2, ISO 27001, PCI DSS) | + | + |
| Effective-permissions analysis on file shares & M365 | + | |
| Excessive-access remediation workflows | + | |
| Sensitive-data discovery & classification | + | |
| Stale-access & toxic-combination detection | + | |
| Real-time alerting on privileged-account misuse | + | |
| Forensic investigation & audit trail | + | |
| Best fit: detective controls, post-incident forensics, compliance reporting | + | |
| Best fit: preventive controls, least-privilege enforcement, M365 Copilot readiness | + |
Most Softprom customers in Poland deploy both products through the unified Netwrix 1Secure platform — Auditor for detection and compliance evidence, Access Analyzer for prevention and least-privilege enforcement.
For partners and customers
For partners — resellers, integrators, MSPs
- Deal registration and margin protection through Softprom's Netwrix partner program.
- Pre-sales technical support from 30+ certified Softprom cybersecurity engineers.
- Demo lab access for live customer demonstrations of 1Secure, Auditor, and Endpoint Protector.
- Marketing development funds (MDF), co-branded campaigns, and lead-sharing.
- Credit lines and contracts in PLN, EUR, USD, and local currencies across 33 countries.
- Multi-tenant Netwrix 1Secure for MSPs serving SMB and mid-market clients in Poland.
For customers — CISO, IT directors, compliance officers
- Free pilot of Netwrix 1Secure modules — DSPM, DLP, PAM, ITDR — in your own environment.
- Compliance mapping for RODO, NIS 2 / KSC, DORA, KNF Rekomendacja D, ISO 27001.
- On-site and remote implementation support in Polish, English, and German.
- Architecture workshops for Active Directory and Microsoft 365 Copilot security.
- Post-deployment health checks and licensing renewals through a single regional point of contact.
- Direct escalation path to Netwrix R&D and global support via Softprom.
Why buy Netwrix from Softprom in Poland authorized distributor
-
Authorized Netwrix distributor
Direct licensing, official support escalation path, and access to the full Netwrix product roadmap and beta programs. -
Local engineering expertise
30+ certified cybersecurity specialists experienced with Polish regulatory frameworks and enterprise Active Directory environments. -
Compliance-led delivery
Every project mapped to RODO, NIS 2 / Ustawa o KSC, DORA, and KNF guidance from day one — not bolted on after deployment. -
26+ years on the market
Value-added IT distributor since 1999 — 90+ cybersecurity vendors, 200+ cybersecurity solutions, 1,000+ active partners. -
Regional reach beyond Poland
14 offices across Central and Eastern Europe, the Caucasus, and Central Asia for multinational deployments and cross-border rollouts. -
Pilot in 2–4 weeks
Most Netwrix 1Secure pilots reach time-to-value within 2–4 weeks; full production deployments typically complete in 30–90 days.
Frequently asked questions
Softprom is an authorized Netwrix distributor in Poland and supplies the full Netwrix product line — including Netwrix Auditor, Access Analyzer, PingCastle, Endpoint Protector, Privilege Secure, Identity Manager, and the 1Secure platform — with local pre-sales, pilots, and engineering support.
Netwrix 1Secure™ is a unified data and identity security platform that combines DSPM, DAG, DLP, AI governance, ITDR, IGA, ISPM, PAM, and directory security in a single control plane — replacing siloed tools with one integrated workflow and one dashboard.
Yes. Netwrix discovers and classifies personal data, tracks who accesses it, audits changes, and produces compliance evidence — supporting RODO obligations (data minimization, access logging, breach response) and UODO reporting requirements with audit-ready reports.
Netwrix 1Secure delivers the identity governance, privileged-access control, continuous monitoring, and incident-detection capabilities required by NIS 2 and Ustawa o Krajowym Systemie Cyberbezpieczeństwa for Operatorzy Usług Kluczowych (OUK) and important entities operating in Poland.
Netwrix Auditor focuses on change auditing and behavior analytics across AD, Microsoft 365, file servers, and databases — a detective control. Netwrix Access Analyzer focuses on effective permissions, access risk, and least-privilege enforcement on sensitive data — a preventive control. Most Polish enterprises deploy both.
Netwrix 1Secure scans SharePoint, OneDrive, and Teams for overshared and unclassified files before Copilot deployment, applies sensitivity labels, enforces least-privilege access, and continuously monitors Copilot interactions for risky data exposure — preventing Copilot from surfacing data employees should not see.
Netwrix supports SaaS, on-premises, and hybrid deployments — including air-gapped environments — making it suitable for Polish banks, public-sector entities, and critical-infrastructure operators with data-residency or sovereignty requirements under KSC and DORA.
Most Netwrix 1Secure pilots run within 2–4 weeks. Production deployments typically reach time-to-value in 30–90 days, with Softprom's certified engineers handling architecture design, integration with Active Directory or Entra ID, and policy tuning.
As an authorized Netwrix distributor, Softprom brings deep expertise in deploying identity-first data security across Polish enterprises, banks under KNF supervision, public-sector OUKs, and managed service providers. Our team is ready to demonstrate how Netwrix 1Secure can replace your siloed identity and data-security tools with a single AI-powered platform — and prove it in a free 2–4 week pilot in your own environment.







 Poland
Poland