Practical Digital Sovereignty on Amazon Web Services: Ensuring Compliance, Continuity, and Control
News | 25.03.2026
Practical Digital Sovereignty: How to Achieve Compliance, Continuity, and Control on Amazon Web Services
Digital sovereignty and sovereign cloud strategies are rapidly gaining importance across industries such as public sector, finance, telecommunications, and healthcare. Organizations are increasingly required to maintain strict control over their data, ensure regulatory compliance, and guarantee operational resilience.
Modern cloud adoption—particularly hybrid and multi-cloud models—reflects the need to balance innovation with data residency and governance requirements. In this context, digital sovereignty is not a theoretical concept but a practical framework for managing risk, compliance, and operational control.
As an official AWS partner, Softprom helps organizations design and implement sovereign cloud strategies aligned with business and regulatory requirements.
What Is Digital Sovereignty?
Digital sovereignty is the ability of an organization to control its data, infrastructure, and digital operations in accordance with legal, regulatory, and operational requirements.
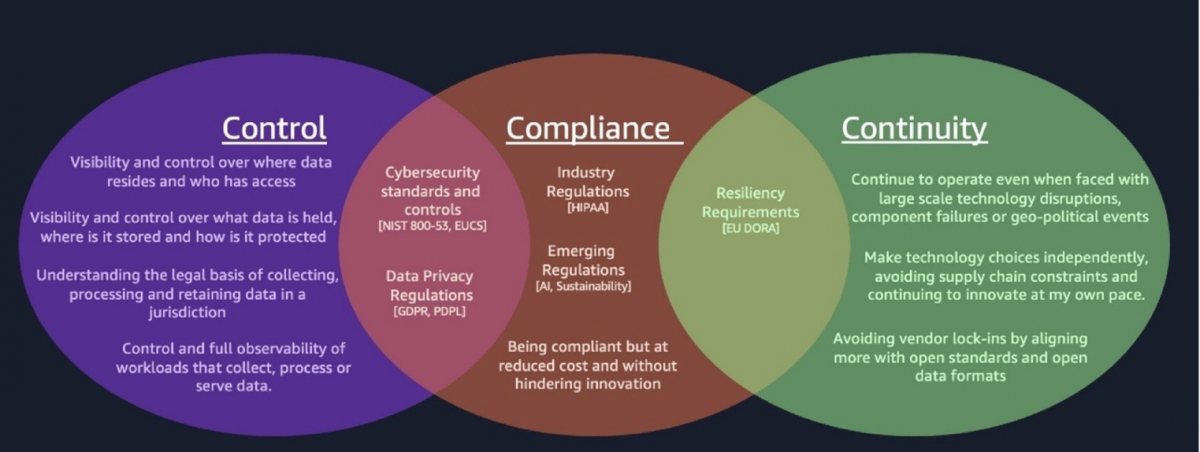
It is built around three core pillars:
- Control – Visibility and governance over data location, access, and processing
- Continuity – Operational resilience and the ability to maintain services during disruptions
- Compliance – Adherence to regulatory frameworks, industry standards, and internal policies
Achieving digital sovereignty requires balancing these pillars while optimizing cost, performance, and scalability.
Understanding Sovereignty Requirements
Before implementing any cloud architecture, organizations must clearly define their sovereignty requirements. This involves:
- Identifying and classifying data (including sensitive and personal data)
- Understanding regulatory obligations (e.g., data residency, cross-border transfers)
- Mapping data flows and ownership
- Establishing accountability through data stewardship
AWS provides multiple infrastructure options to support these needs, including Regions, Local Zones, Outposts, and dedicated sovereign environments.
To support governance and visibility, organizations can leverage services such as:
- Data discovery and classification tools
- Centralized data catalogs
- Identity and access management systems
- Multi-account governance frameworks
Implementing Control in Sovereign Architectures
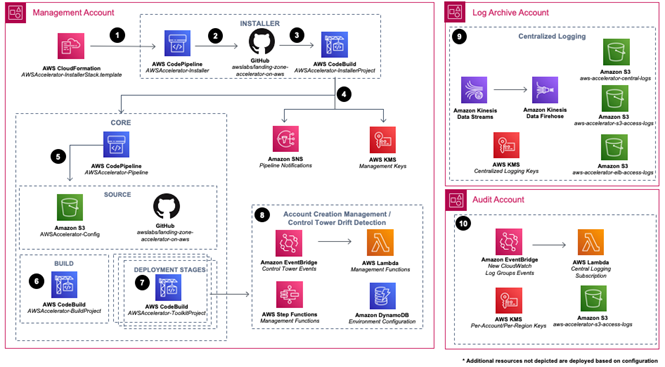
1. Establish a Strong Foundation
A secure landing zone is critical for enforcing governance, compliance, and operational standards across cloud environments. This includes:
- Multi-account structure
- Centralized policy enforcement
- Preventive and detective controls
2. Data Protection and Encryption
Sensitive data must be protected both at rest and in transit using robust encryption strategies. Key considerations include:
- Centralized key management
- Hardware-based security modules for high-assurance workloads
- External key control for regulated environments
3. Access Governance
Clearly defined ownership and access policies are essential for maintaining accountability and preventing unauthorized access. This includes:
- Role-based access control
- Fine-grained permissions
- Identity federation and authentication controls
4. Data Movement Monitoring
Organizations must track and log data flows across systems and boundaries to ensure compliance with residency requirements. This includes:
- Network traffic monitoring
- API activity tracking
- Logging and audit trails
5. Automated and Enforceable Controls
Embedding compliance into CI/CD pipelines and infrastructure provisioning ensures that non-compliant resources are never deployed. This includes:
- Policy-as-code
- Automated compliance checks
- Real-time remediation workflows
Continuous Monitoring and Compliance
Maintaining sovereignty requires continuous validation of controls and compliance posture.
Key practices include:
- Mapping regulatory requirements to technical controls
- Automating evidence collection for audits
- Detecting and remediating non-compliant resources
- Maintaining immutable audit logs for forensic analysis
AWS services enable centralized monitoring, compliance dashboards, and automated remediation, helping organizations maintain continuous compliance at scale.
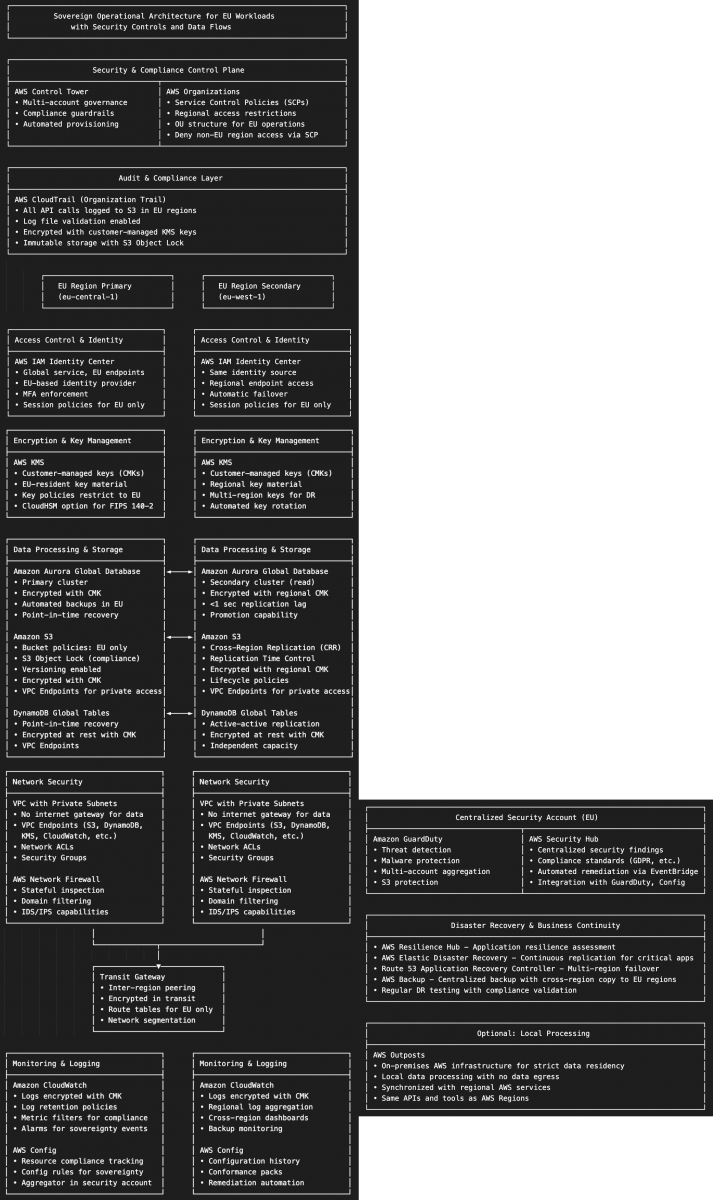
Ensuring Continuity (Operational Sovereignty)
1. Survivability
Organizations must maintain operations during large-scale disruptions, including outages, cyberattacks, or geopolitical risks. This requires:
- Multi-region and multi-AZ architectures
- Local processing capabilities
- Controlled failover mechanisms
2. Resilience
Systems should automatically handle common disruptions such as traffic spikes or component failures through:
- Auto scaling
- Load balancing
- Distributed architectures
3. Operational Independence
Organizations must retain control over operations within defined jurisdictions, including:
- Regional governance
- Independent identity and access control
- Auditable operational processes
4. Infrastructure and Data Management
Sovereign architectures require strict control over where data is stored and processed, supported by:
- Multi-site deployments
- Local infrastructure options
- Controlled replication strategies
5. Recovery and Testing
Regular testing of disaster recovery scenarios ensures readiness and compliance. Automated recovery processes must respect sovereignty constraints.
6. Portability and Interoperability
To avoid vendor lock-in and ensure flexibility, organizations should design workloads using:
- Open standards
- Containerization
- Modular architectures
Implementing Compliance
Compliance Strategy
Organizations must manage overlapping regulatory, industry, and contractual requirements. A compliance matrix helps map these obligations to technical controls and processes.
Key Components
1. Monitoring and Remediation
Continuous monitoring of infrastructure, data flows, and configurations enables rapid detection and response to compliance issues.
2. Audit Readiness
Maintaining immutable logs, automated evidence collection, and audit workflows ensures readiness for regulatory inspections.
3. Secure Processing
Hardware-level isolation and encryption provide strong guarantees for data protection during processing, supporting strict regulatory requirements.
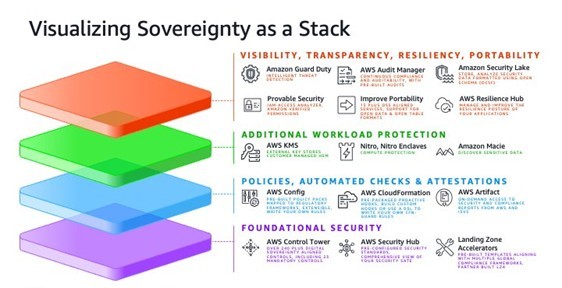
The Digital Sovereignty Stack
Digital sovereignty can be visualized as a layered architecture that integrates:
- Infrastructure and data residency controls
- Security and encryption mechanisms
- Governance and compliance frameworks
- Monitoring and observability tools
- Automation and remediation capabilities
These layers work together to support the three pillars: control, continuity, and compliance.
Conclusion
Digital sovereignty is no longer optional—it is a critical requirement for organizations operating in regulated and data-sensitive environments. Achieving it requires a structured approach that integrates governance, security, compliance, and operational resilience.
AWS provides a comprehensive set of services and architectural patterns to support sovereign cloud implementations. However, successful adoption depends on proper design, governance, and continuous optimization.
As an official AWS partner, Softprom supports organizations at every stage of this journey—from assessing regulatory requirements and designing sovereign architectures to implementing and managing compliant, resilient cloud environments.
By adopting a practical approach to digital sovereignty, organizations can unlock the full value of cloud innovation while maintaining control, compliance, and operational continuity.







